- Services
Services
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Solutions
Solutions
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Products
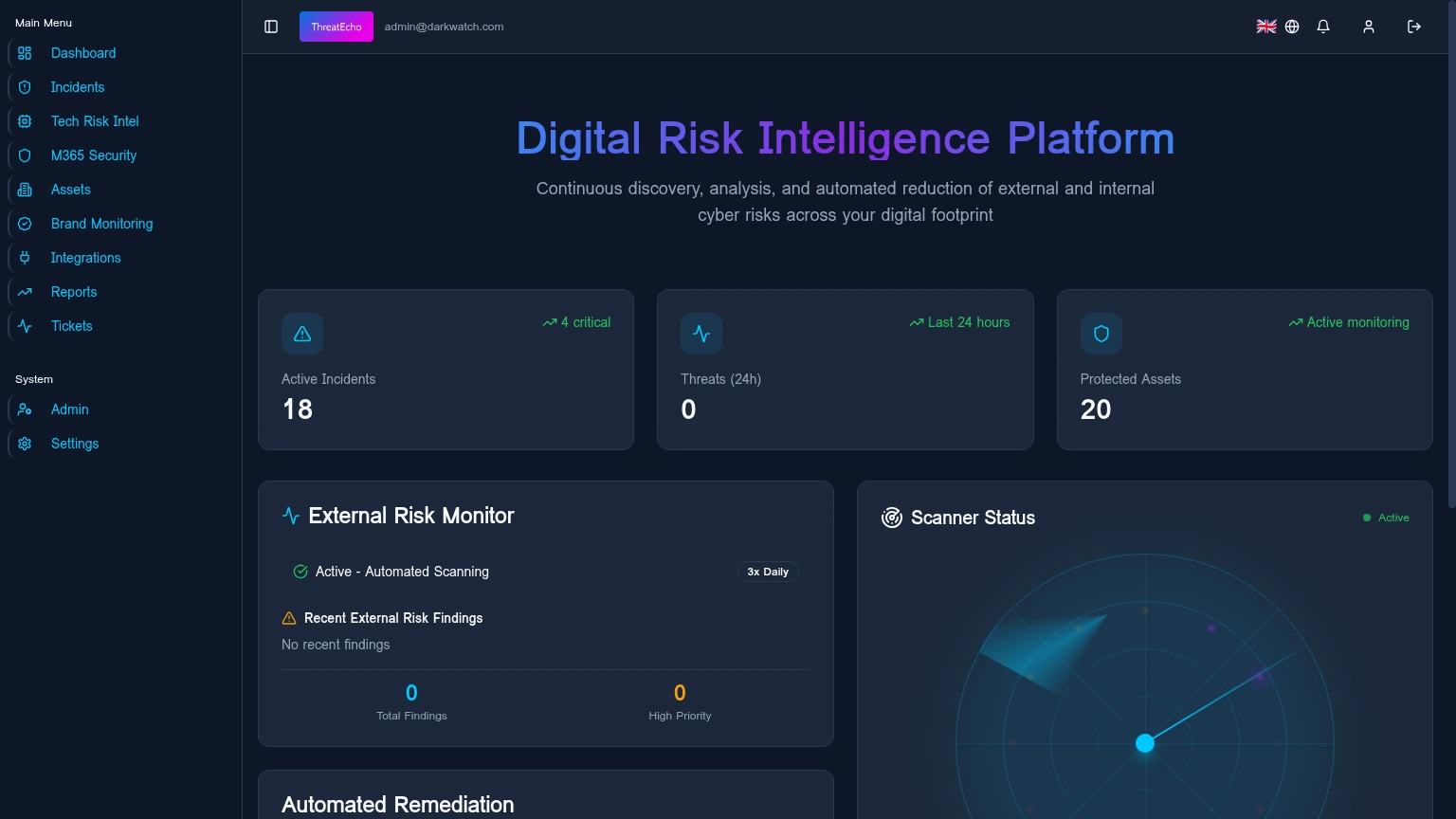
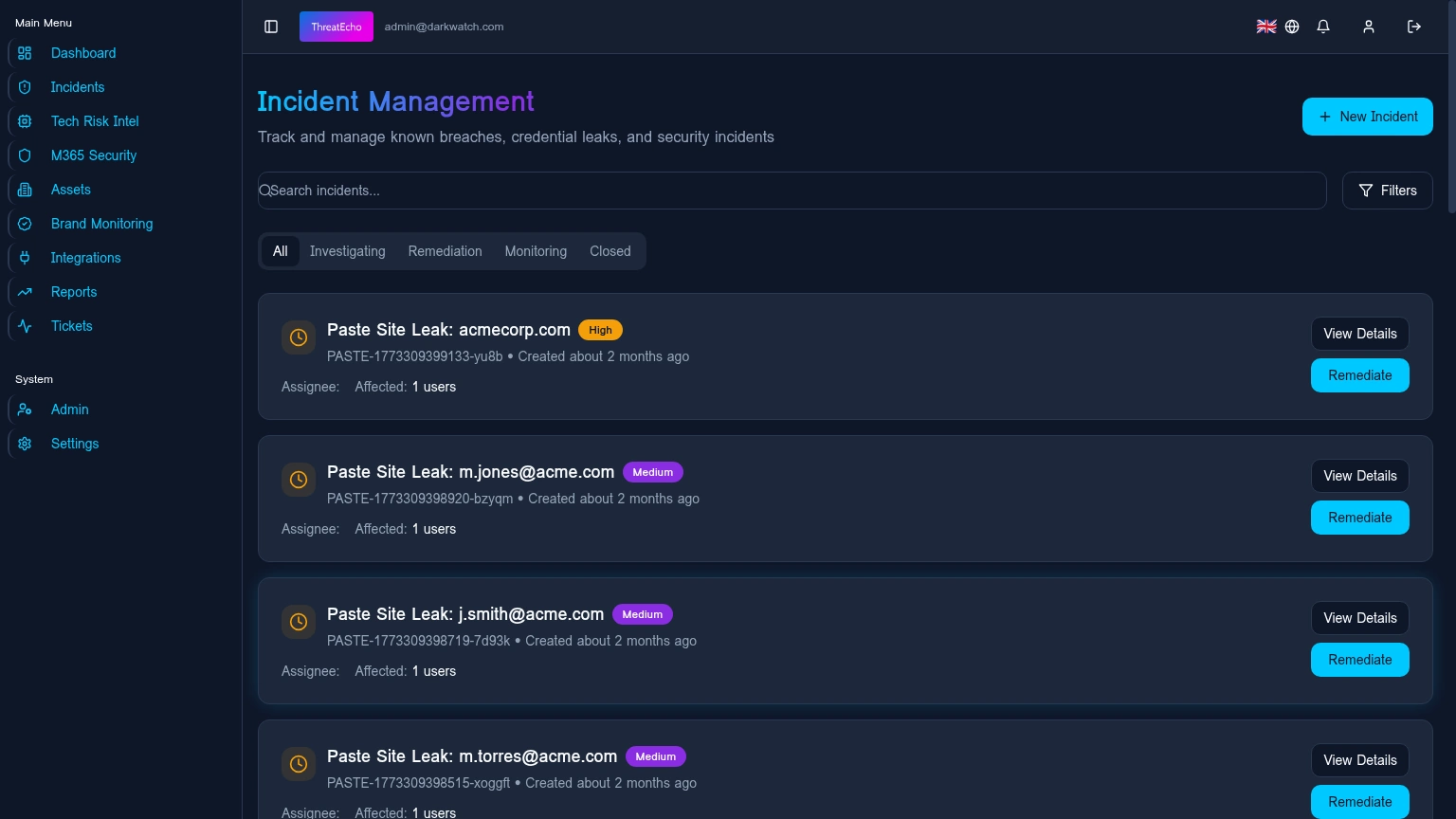
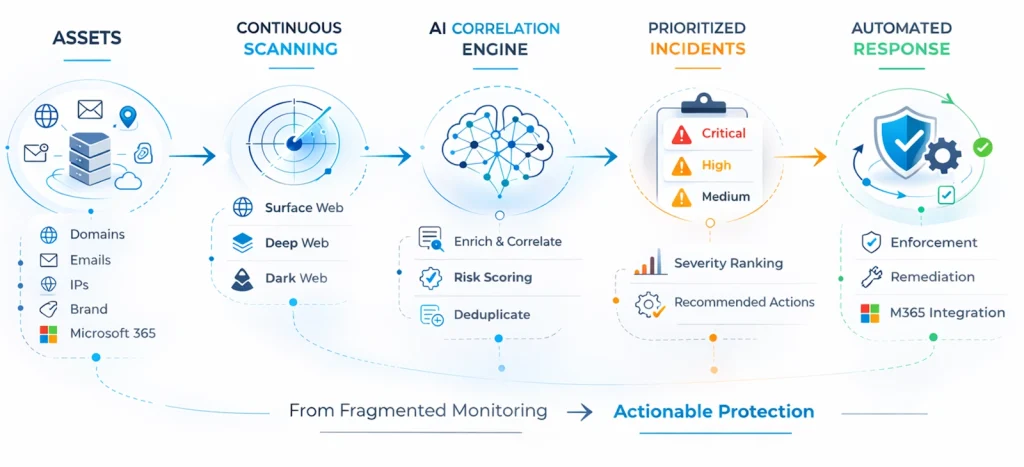
Proprietary Products
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Partners
Partners
In the current, complex and dynamic context of cyber security, collaboration with partners is of strategic importance for Safetech Innovations. This section presents our partnerships for integrated solutions and provides information to our resellers of our own and distribution channel products.
- Customers
Customers
Safetech Innovations S.A. has been providing cyber security services and solutions tailored to the needs of organizations since 2011. Many Romanian organizations have chosen Safetech's solutions and services for system integration, consulting, vulnerability management, operations outsourcing, security audit, in order to improve their level of cyber security.
- Investors
Investors
On Feb. 6 2023 Safetech Innovations shares started trading on the Main Market of the Bucharest Stock Exchange under the symbol SAFE. This section contains information and documents intended for SAFE investors. For information on the evolution of share prices, we invite you to follow our profile on the BVB website.
- Company
Company
Since 2011, we have maintained our strategic focus on cyber security, we act as a Managed Security Service Provider, and to date we have completed more than 600 testing and consulting projects and participated in more than 100 critical infrastructure security projects in the United States United, EU, China, India, Canada, Brazil, Morocco, Singapore, Philippines and New Zealand.
- News
- Contact

- Services
Services
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Solutions
Solutions
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Products
Proprietary Products
Make sure your organization is safe and let us design the best action plan for your company's cybersecurity needs.
- Partners
Partners
In the current, complex and dynamic context of cyber security, collaboration with partners is of strategic importance for Safetech Innovations. This section presents our partnerships for integrated solutions and provides information to our resellers of our own and distribution channel products.
- Customers
Customers
Safetech Innovations S.A. has been providing cyber security services and solutions tailored to the needs of organizations since 2011. Many Romanian organizations have chosen Safetech's solutions and services for system integration, consulting, vulnerability management, operations outsourcing, security audit, in order to improve their level of cyber security.
- Investors
Investors
On Feb. 6 2023 Safetech Innovations shares started trading on the Main Market of the Bucharest Stock Exchange under the symbol SAFE. This section contains information and documents intended for SAFE investors. For information on the evolution of share prices, we invite you to follow our profile on the BVB website.
- Company
Company
Since 2011, we have maintained our strategic focus on cyber security, we act as a Managed Security Service Provider, and to date we have completed more than 600 testing and consulting projects and participated in more than 100 critical infrastructure security projects in the United States United, EU, China, India, Canada, Brazil, Morocco, Singapore, Philippines and New Zealand.
- News
- Contact