Strengthening OT Security and alignment to NIS2 with advanced Radiflow360 solutions and Safetech expertise
Strengthening the security of critical OT/SCADA infrastructures is imperative for two seemingly different but deeply convergent reasons. On the one hand, there is the need for compliance with the NIS2 Directive, a legal requirement that can no longer be ignored. On the other hand, the reality on the ground is worrying: 60% of the organizations analyzed have experienced at least one cybersecurity incident in OT environments in the last 12 months, and half of them have faced multiple attacks (according to XOne Networks Annual OT/ICS Cybersecurity Report ).
This duality is difficult to manage internally by most organizations, mainly due to the lack of adequate cybersecurity tools, but also the lack of expertise and specialized human resources. The same report highlights that, despite the increase in the number of teams dedicated to OT security, they remain under significant pressure, generated by the complexity of managing hybrid environments, in which legacy systems and modern technologies coexist.
Safetech Innovations is aimed precisely at these organizations, which manage complex OT infrastructures, but have difficulty securing them according to NIS2 requirements and often end up tolerating a high level of risk. In many cases, this situation is compensated by the use of existing teams and outdated technological solutions.
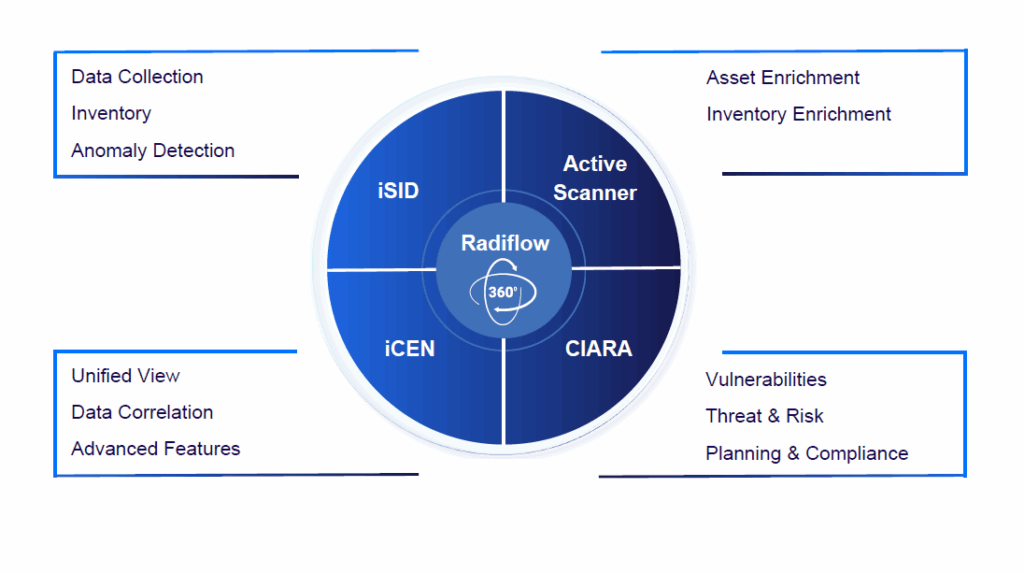
A mature solution in Safetech’s portfolio, Radiflow360, represents a next-generation platform for OT security, enhanced with artificial intelligence capabilities. It provides complete visibility into infrastructure, risk management and effective incident response, and is designed specifically for medium-sized industrial organizations.
By integrating previously disparate tools and manual processes into a unified platform, Radiflow360 enables OT security teams to gain real-time control over operational environments while simplifying incident detection, analysis, and response processes.
High complexity, limited resources, and new types of threats
Most organizations operating OT infrastructures face a difficult combination of factors:
- Legacy systems coexisting with modern technologies
- Lack of dedicated tools for OT security
- Shortage of specialized skills in industrial cybersecurity
- Operational pressure that limits intrusive changes.
Although the number of teams dedicated to OT security is growing, they remain overworked, trying to manage increasingly complex hybrid environments with limited resources. As a result, many organizations end up tolerating a high level of risk, failing to adequately respond to current challenges.
In parallel, the OT security landscape is marked by a paradigm shift: attackers are no longer just targeting data, but physical processes, with a direct impact on operations. Dominant trends include:
- 332% increase in exposed OT devices (over 20 million accessible online)
- Attacks aimed at physically disrupting systems
- Using AI Agents to discover vulnerabilities
- Indirect attacks on support infrastructures (identity, virtualization, HMI)
- Exploiting supply chain access
- Industrial-grade ransomware with a focus on critical downtime.
This development makes alignment with the NIS2 Directive no longer just a legal obligation, but an essential condition for ensuring operational continuity and reducing critical risks.
Why organizations choose Radiflow360 for NIS2
For organizations operating critical OT/SCADA infrastructures, alignment with the requirements imposed by the NIS2 Directive is no longer just a formal obligation, but a complex process that requires visibility, control, and the ability to make quick decisions in a sensitive operational environment. In this context, the adoption of an integrated platform like Radiflow360 directly addresses these needs.
In practice, organizations pursue three essential objectives when implementing Radiflow:
- Gain complete visibility into OT infrastructure, including legacy systems
- Implementation of continuous risk management, correlated with the impact on industrial processes
- Ensuring early detection of incidents, complemented by robust reporting and auditing capabilities.
Beyond these objectives, the adoption decision is influenced by a series of clear operational advantages, validated in real implementations:
- Solution natively designed for OT environments, not later adapted from IT
- Non-intrusive monitoring with no impact on business continuity
- Risk-based approach aligned with NIS2 requirements
- Integration of visibility, detection and evaluation functions in a single platform
- Audit- and compliance-ready reporting capabilities.
A major differentiator of Radflow solutions is the complete coverage of the OT security lifecycle, in a unified model that eliminates fragmentation of tools and processes:
- Identify – mapping OT assets and assessing risks according to their importance in the business
- Protect – providing relevant information to existing security solutions (firewall, NAC, SRA)
- Detect – passive traffic monitoring and identification of anomalies or unauthorized commands
- Respond – prioritizing alerts and using playbooks for quick response
- Govern – auditing, reporting and alignment with standards such as NIS2, NIST or IEC.
This integrated approach is supported by the consolidation of advanced detection and analysis capabilities with the risk management functionalities offered by Radiflow CIARA, resulting in unified visibility into the entire OT ecosystem – from assets and vulnerabilities to response actions.
In addition, Radiflow360 integrates an AI Analyst Assistant, which brings a significant operational advantage, especially in the context of the shortage of specialized skills:
- Prioritize threats using contextual intelligence
- Accelerates incident investigation processes
- Provides actionable recommendations to increase resilience.
Through this combination of visibility, automation and artificial intelligence, Radiflow360 becomes a true “command center” for OT security, giving organizations not only NIS2 compliance, but also real control over risks that can directly affect industrial processes.
How the Radiflow360 solution works in practice. Main components
In practice, the efficiency of a platform like Radiflow360 comes from the way each component contributes specifically, but complementary, to the security and compliance requirements imposed by the NIS2 Directive. The architecture is designed as a logical flow, in which visibility, control and risk analysis are progressively built.
1. Radiflow iSID – OT Visibility and Incident Detection
In most projects, iSID is the first element implemented, as it responds to a fundamental need: a real understanding of the OT environment. In many organizations, this visibility is incomplete or fragmented, especially in the presence of legacy systems.
iSID automatically discovers equipment in the network and builds an updated inventory of assets, without affecting operations. Through in-depth analysis of industrial traffic (including at the level of specific protocols), the solution identifies behavioral deviations that may indicate incidents or attack attempts. At the same time, it monitors configuration changes in PLCs and highlights existing vulnerabilities in industrial equipment.
Operationally, this translates into:
- A clear and up-to-date view of all OT assets
- Early detection of anomalies and unauthorized orders
- Automatic incident alerting and prioritization
- Generating the network topology (Purdue model), essential for understanding industrial flows.
Through these capabilities, iSID directly covers NIS2 requirements such as asset inventory, continuous monitoring, incident detection, and vulnerability management, becoming the foundation of any OT security strategy.
2. Radiflow iCEN – Centralization, Governance, and Reporting
Once visibility is achieved locally, iCEN brings control to the organizational level. It is the component that transforms disparate data into coherent and actionable information, especially in organizations with distributed infrastructures or multiple locations.
iCEN centralizes alerts from different iSID instances and correlates them in a unified picture. Thus, security teams no longer operate in silos, but benefit from a consolidated perspective on risks. The risk scores generated for each location allow interventions to be prioritized, and access control and audit mechanisms facilitate compliance with governance requirements.
In practice, customers capitalize in particular:
- Centralized dashboards with risk scores by location
- Consolidating and matching alerts from multiple sources
- Planning and monitoring of risk assessments
- Analysis of the evolution of risks over time.
This component responds directly to NIS2 requirements related to audit, reporting, and operational security management, providing clear and scalable governance.
3. CIARA – Risk Management and Compliance
If iSID provides visibility and iCEN provides control, CIARA is the component that brings decision-making intelligence. It is frequently used in compliance projects because it allows for rigorous and continuous risk assessment.
CIARA uses the data collected from the infrastructure to build a digital model of the OT environment and simulate real attack scenarios. Instead of a simple list of vulnerabilities, organizations get a clear picture of the potential impact on industrial processes – which systems are critical, what effects an incident would have, and where to intervene as a priority.
Functionally, this means:
- Continuous assessment of risk and attack vectors
- Linking vulnerabilities to operational impacts
- Mapping controls to relevant standards (including NIS2, IEC 62443, NIST)
- Evolutionary risk analysis for continuous improvement.
Through this approach, CIARA enables organisations to move from reactive to proactive, risk-based security – an explicit requirement of the NIS2 directive.
NIS2 Requirement | Radiflow functionality | Component |
Risk management | Continuous risk assessment | CIARA |
Incident detection | Anomaly and OT incident detection | iSID |
Continuous monitoring | Passive monitoring of OT traffic | iSID |
Asset inventory | Automatic asset discovery | iSID |
Vulnerability Management | Vulnerability identification + risk analysis | iSID + CIARA |
Reporting and Auditing | Centralized reporting and auditing | iCEN |
Multi-site governance | Centralized management and risk scores by location | iCEN |
Business impact analysis | Attack simulation and operational impact assessment | CIARA |
Continuous improvement | Risk Evolution Analysis and Continuous Optimization | CIARA + iCEN |
Together, the three components define a coherent operating model: iSID provides visibility and detection, iCEN brings control and governance, and CIARA transforms data into strategic decisions. This type of correlation is essential in real projects, as it helps organizations translate abstract NIS2 requirements into concrete and measurable technical capabilities.
Why organizations choose to work with Safetech Innovations to strengthen OT Security and align with NIS2
Organizations operating critical infrastructures choose to collaborate with Safetech Innovations not only for technology, but for the ability to deliver implementations adapted to the complex realities of OT/SCADA environments and to concretely support alignment with the NIS2 Directive.
The experience gained in critical industrial projects – where the availability and continuity of processes are essential – has imposed a rigorous, carefully calibrated approach for each infrastructure. In such environments, any intervention must be predictable and non-intrusive, which is why Safetech has consistently applied industry-validated best practices: passive monitoring of industrial traffic, minimizing the impact on production systems and aligning security measures with the operational requirements specific to SCADA environments.
This experience translates, in practice, into a real ability to adapt. Each OT environment comes with its own constraints – from legacy systems that are difficult to update to critical processes that do not allow for interruptions – and security solutions must be configured accordingly. Safetech designs and implements robust yet discrete architectures that increase the level of security without affecting operations.
As a partner for Radiflow360, the company offers a complete set of services, from design and implementation to operation and continuous optimization. These services target not only compliance, but also operational resilience, allowing organizations to reduce their risks and optimize their security investments.
Specifically, Safetech ensures:
- Implementation of the platform in local or centralized architectures, depending on the specifics of the infrastructure
- Integration with other existing technology platforms (SIEM, IAM, network solutions)
- Adapting configurations to operational and compliance requirements
- Support in operation and continuous improvement of the security posture.
The result is an end-to-end approach, in which technology is supported by practical expertise, and compliance with NIS2 becomes a controlled, sustainable process aligned with business objectives.
For additional information, please contact us at sales @ safetech.ro or by phone +40 21 316 0565.